This page is still to be updated...
Digital Forensic Challenge Images (Datasets)
This page contains all the digital forensic challenges (datasets) I prepare either for a training course I teach, a DFIR challenge done @Security4Arabs, testing an application or written code, or just for fun! The current challenges are: Challenge #1, Challenge #2, Challenge #3, Challenge #4, Challenge #5, Challenge #6, Challenge #7, Challenge #8, Challenge #9, Challenge #10, Challenge #11, Memory Forensics #01, UNALLOCATED Disk Space #01, and different Linux Forensic Cases. More will be added soon, so keep checking the site for updates.
Note: if you have any comments or notes, please don't hesitate to contact me, I will do my best to get back to you ASAP. Also, if you use any of my work for your training, presentation, etc, I would appreciate if you inform me. Don't worry, I won't charge you anything, and use them for free as you like. I just want to be informed for referencing purposes only.
Challenge #1 - Web Server Case
- System Image: here
- System Memory: here
- Hashes: here
- Passwords = here
- Other download URLs from (Archive.org) could be found here: here
- What type of attacks has been performed on the box?
- How many users has the attacker(s) added to the box, and how were they added?
- What leftovers (files, tools, info, etc) did the attacker(s) leave behind? (assume our team arrived in time and the attacker(s) couldn’t clean and cover their tracks)
- What software has been installed on the box, and were they installed by the attacker(s) or not?
- Using memory forensics, can you identify the type of shellcode used?
- What is the timeline analysis for all events that happened on the box?
- What is your hypothesis for the case, and what is your approach in solving it?
- Is there anything else you would like to add?
Challenge #2 - User Policy Violation Case
- System Image: here
- Hashes & Password: here
- Other download URLs from (Archive.org) could be found here: here
- File Carving, Custom Carving, and Keyword Searching
- File System Forensics - NTFS
- Deep Windows Registry Forensics: System and User Hives
- SYSTEM
- SOFTWARE
- SAM
- NTUSER.DAT
- USRCLASS.DAT
- Other Windows Files: LNK, Jump Lists, Libraries, etc
- Application Compatibility Cache (ShimCache)
- Analyzing Windows Search (Search Charm)
- Analyzing Thumb Caches
- Analyzing Prefetch Files
- Analyzing Recycle Bin(s)
- USB Forensics
- Events Analysis
- Email Forensics: Web and Outlook
- Browser Forensics: Internet Explorer and Google Chrome
- Skype Forensics
Challenge #3 - Mystery Hacked System
- System Image: here
- Hashes: here
- Password = here
- Other download URLs from (Archive.org) could be found here: here
- How was this system hacked? (What is your hypothesis)
- What evidence did you find that proves your hypothesis?
- How did you approach and solve the case? (write a report)
- Anything you would like to add?
Challenge #4 - Launching Attacks from Alternate Data Streams
This is another digital forensics image that was prepared for to test the following:
- Hidding EXEs in ADS
- Running Malicious EXEs from ADS
- Checking if Windows Defender (or other AVs), truly scan ADS
- Hiding Malicious EXEs in Stealthy ADS
- Showing How all of the above methods could be detected
- Forensic Image: here
- Hashes: here
- File List: here
- Other download URLs from (Archive.org) could be found here: here
Challenge #5 - BSides Amman 2021 2nd Edition / Windows Forensics Workshop Case
- What is the hash value for the given forensic image?
- Which user account was used to access some confidential documents?
- Explain in detail what proof do you have to support your answer?
- Did the user access the confidential files from a local drive or network location?
- What proof do you have to support your answer?
- List all the files that were accessed with full paths.
- Provide two different evidence to prove that those files were truly accessed.
- Which application was used to open any of the confidential document(s)? The next three questions are related to the image with the text "AnotherPassword4U" found inside the user's home directory.
- What is the full path to the files of interest?
- What is the Volume Serial Number where the file exists?
- What are the Modified, Accessed, and Creation (MAC) timestamps in UTC for the file? The DCode.exe application was used by one of the users. Provide evidence to the next four questions below, but, be careful, this is a tricky question!!!
- Which user do you think ran the application and what evidence do you have to support your hypothesis?
- How many times was it used?
- When was it last used?
- Where was the application located (full path)?
Challenge #6 - Browser Policy Violation Case
- Files could be found: here
Challenge #7 - SysInternals Case
Challenge #8 - NTFS File System Case
- E01 for the drive could be found: here
- There are 5 hidden things for you to find!
- Explain how these files were hidden
- For more detailed instructions, please check this case under cases at here
Challenge #9 - Encrypt Them All Case
- E01 for the drive could be found: here
- #1: Lost in Space:
We noticed that the whole communication started with a README file within the users documents directory. Unfortunately, this file seems to be encrypted with AES and we do not have the password to decrypt it. You would either need to search the cache for the communication or try to recover the file before it was encrypted. It seems this file leads to the solution of our next requirement.
- #2: Do Not Be Deceived!:
It seems Jane has been using a volume with full disk encryption (Bitlocker). It has been applied to a volume named R2D2. You are required to decrypt this volume and find what was hidden within it.
- #3: "Your Focus Determines Your Reality.":
One of the messages sent to the unknown part seemed to be using asymmetric encryption with a Public/Private key. Since we were able to acquire an image of Jane’s system, you should be able to extract these keys and use them to decrypt the message. The message which has been shared with our unknown third party, is within the keys file within the user’s download directory. You need to decrypt this file in order to get the secret message. Do you know what this was used for?
- For more detailed instructions, please check this case under cases at here
Challenge #10 - Meeting Location Case
- E01 for the drive could be found: here
- Deliverable #1: Where is the Evidence?
You need to find answers with explanations to the following:
- What is Max using to hide his activity?
- Find and restore the methods/tools/techniques/etc that he is using. Note: This might require data recovery/carving
- Deliverable #2: Where are they Meeting?
After you have found the methods that Max has been using to hide his tracks, you are required to:
- Find out what Max was searching for based on analyzing the browser history.
- We believe that Max received the information about the meeting location in an encrypted file. Search for that file and after decrypting the file (if needed), determine the meeting location.
- What was the name of the file that has the meeting location?
- From where did Max get the meeting location (URL, chat, email, etc)?
- Deliverable #3: Reflection
Reflect on what you learned from this case.
- For more detailed instructions, please check this case under cases at here
Challenge #11 - Where Did Administrator Go?
- You are required to find what happened to this system and how?
Memory Forensics #01 - RansomCare Investigation Case 1
- E01 for the Memory Dump could be found: here
- Find RansomCare's code, dump it. and explain what happened to the victim system.
- $100 bounty for whoever is able to solve this case.
- For more details on RansomCare's capabilities, please check our adversary simulation system "TARIQ" at here
Unallocated Disk Space #01 - Investigation Case 1
- The UNALLOCATED Disk Space file can be found: here
- Use all your skills to investigate and explain what happened to the victim's system.
- For more detailed instructions, please check this case under the Data Recovery Course at CYBER 5W
Linux Forensic Cases
These are four different cases to cover Linux forensic investigations and a brief could be found below:
- Case1: Compromised Web Server
- Case2: Compromised Hadoop (HDFS) Cluster
- Case3: Attacker's Kali Linux System
- Case4: Investigating/Hunting Hidden Processes
A company’s web server has been breached through their website. Our team arrived just in time to take a forensic image of the running system and its memory for further analysis. All of the case files can be found here. Old upload could be found below (I'm using them as an alternative now):
Important Note: do not use commercial tools for your own learning benefit.
End of Case.
This is another digital forensics image that was prepared to cover a full Windows Forensics course.
This image covers most if not all of the recent system artifacts that you might encounter. Let me know if you need any help or if you are an instructor and want the answers to each part of the case. I will only send the answers to verified instructors.
End of Case.
This is another digital forensics image that was prepared to for a Windows and File System Forensics course. This is a little of a mystery,
so I won't be giving out too much clues about what you can learn in this case, but I assure you, you can learn a lot ;)
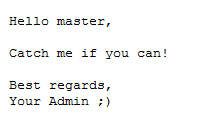
One day an IT dept. guy/gal came to work to find the message below written in a file on his/her system!
He/Her immediately reported that to you. Now you must:
End of Case.
End of Case.
CASE OVERVIEW: You have been given a system that has been used for some illegal activity were the user accessed confidential files that the user was not supposed to access. The system has two user accounts which are the main suspects involved in this case ("joker" and "IEUser"). You are required to provide answers to all the questions below by providing evidence (proof) with details and screenshots. Remember: SCREENSHOT OR IT DID NOT HAPPEN ;)
All of the case files can be found here.
They can also be found here and here too.
To successfully solve this challenge, a report with answers to the tasks below is required:End of Case.
This is another digital forensics image that was prepared to cover Windows and Browser Forensic Artifacts.
End of Case.
The user downloaded what they thought was the SysInternals tool suite, double-clicked it, but the tools did not open and were not accessible. Since that time, the user has noticed that the system has "slowed down" and become less and less responsive.
Special Thanks to Harlan Carvey for helping form this case. Please check his amazing work here.
End of Case.
In this case you are required to find all the data and files that have been hidden using some of the NTFS file system capabilities.
End of Case.
In this case you are required to decrypt all the data and files that have been encrypted using different crypto methods.
End of Case.
Our suspect Max, seems to be part of a foreign intelligence group and our intelligence team has been tracking him for months now. It seems Max has agreed to meet with an unknown party at some location. After Max left his apartment, we were able to acquire an image of his system. Unfortunately, when we did our investigation, we did not find anything. We are sure that Max has no other system and this is the only system he uses. We need your help with this investigation. The faster you are able to retrieve the info, the quicker we will be able to stop their next operations.
End of Case.
The ThreatSim domain administrator's files are gone and we do not know what happened or how!
End of Case.
In this case you are required analyze a memory dump of a Windows 10 Pro system that has been hit with RansomCare.
End of Case.
We have a system that has been compromised by a malware and the only evidence we have is the system's Unallocated disk space!
End of Case.
End of Summary.